SafeBPF: Hardware-assisted Defense-in-depth for eBPF Kernel Extensions
 An overview of SafeBPF architecture
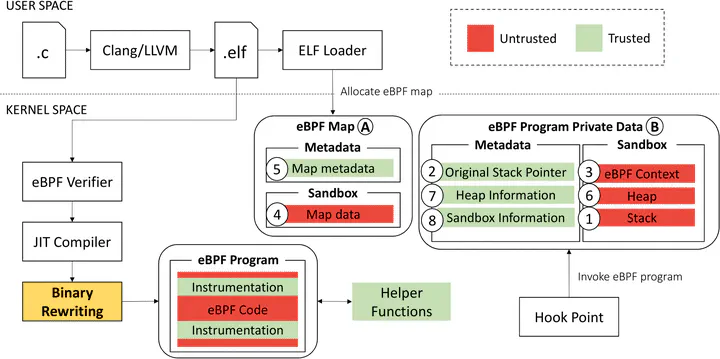
An overview of SafeBPF architectureAbstract
The eBPF framework enables execution of user-provided code in the Linux kernel. In the last few years, a large ecosystem of cloud services has leveraged eBPF to enhance container security, system observability, and network management. Meanwhile, incessant discoveries of memory safety vulnerabilities have left the systems community with no choice but to disallow unprivileged eBPF programs, which unfortunately limits eBPF use to only privileged users. To improve run-time safety of the framework, we introduce SafeBPF, a general design that isolates eBPF programs from the rest of the kernel to prevent memory safety vulnerabilities from being exploited. We present a pure software implementation using a Software-based Fault Isolation (SFI) approach and a hardware-assisted implementation that leverages ARM’s Memory Tagging Extension (MTE). We show that SafeBPF incurs up to 4% overhead on macrobenchmarks while achieving desired security properties.
Type
Publication
In Cloud Computing Security Workshop (CCSW)
The SafeBPF patch is available for download by clicking the CODE button above. The patch includes software-based isolation on both the x86 and ARM architecture, and hardware-assisted isolation on ARM. For more information about our software artifact, please refer to the paper or contact me via email.